The Perimeter Is the Purpose: Hardening the Sovereign Road Against the Inverted Trust
A Compass Heading for the mature convoy — those who have established their foundation and are ready to implement the structural exit.
The last article ended with a pencil.
Not a weapon. Not a manifesto. A pencil — assembled across a global supply chain that no single mind planned and no government approved, representing the spontaneous order of free people making free choices.
The point was geometric: the agora exists at the perimeter of the yin-yang, not inside either force. The sovereign exit is not a third political option. It is a structural departure — follow the S-curve outward until you are standing on the circumference, facing open space.
That article was a compass heading. This one is the next bearing — for those who have already run the calculation and are now asking: fine, but what does hardening actually look like?
Because if the first article was about the architecture of exit, this one is about the integrity of the walls.
A perimeter without engineering is just a boundary on paper. The toll booths are real. The people who built them are watching. And some of them have more than a tollgate at their disposal.
I. The Trust Has Been Inverted — And There Is a Paper Trail
To understand why the hardening matters, you have to understand what you are hardening against. Not an abstraction. Not "the government" as a political sentiment. A specific structural violation — one with a documented precedent.
The previous article named the original hierarchy: Natural Law → The People (Beneficiaries) → The State (Trustee/Servant). This is not a political opinion. It is the stated architecture of the American compact — the foundational design that the Declaration, the Constitution, and a century of legal precedent built on top of.
Trustees do not own. They manage. On behalf of the principals. That is the only authority they have — delegated, limited, and revocable.
Now consider a specific document.
On May 27, 1940, President Franklin D. Roosevelt issued Proclamation 2402. The proclamation formally recognized, in its operative language, the "Sovereign Citizens of our Nation" — a phrase that appears not as rhetoric but as the operative description of who, exactly, the government was purporting to protect. The people are named as sovereign. The state is acting on their behalf. The hierarchy is explicit, on the record, in a presidential proclamation.
Hold that document next to the regulatory language being drafted today — across jurisdictions, across administrations, across party lines — and the contrast is not subtle.
The current trajectory of digital regulation does not treat the internet as a public commons. It treats it as a Register-to-Play enclosure. A managed territory where access is conditional, identity is required at the gate, and the terms of entry can be revised at any point by the people administering the gate. The proposed architecture for Digital IDs — some versions of which would tie a national identity number to basic internet access — is not a security measure. It is a conversion: converting a commons into a licensed space. Converting beneficiaries into account holders. Converting the sovereign citizens named in Proclamation 2402 into users of a platform they do not own.
When a Trustee begins to manage the estate not for the Beneficiary's benefit but for the Trustee's — when the servant starts charging the principal rent to enter their own house — the technical term in trust law is breach of fiduciary duty.
The proposed "Kill Switch" frameworks — legislation in various forms that would authorize a governmental executive to shut down or throttle significant portions of internet infrastructure during a declared "national emergency" — are the same breach expressed in technical language. The emergency is always justified. The emergency is always temporary. The emergency is the mechanism by which the permanent transfer of authority is accomplished.
The Trustee has not yet pulled the switch. That is not evidence that the switch does not exist. It is evidence that they have not yet decided the circumstances warrant it.
The perimeter you are building is not a response to paranoia. It is a response to a paper trail.
II. The Garrett Fallacy — Why "Smart Guys Will Figure It Out" Is a Physical Problem
There is a common reflex among technically literate people when these conversations arise. Call it the Garrett position: "Look, the internet is resilient by design. Smart programmers will always find a workaround. You can't really shut it down."
This reflex is not stupid. It is historically well-grounded, up to a point. The original ARPANET architecture was specifically designed to route around damage — to find alternate paths if a node was severed. The web has repeatedly demonstrated an ability to absorb censorship attempts at the application layer, as mirrors multiply faster than they can be removed and VPNs proliferate across jurisdictions.
But the Garrett position contains a category error: it confuses the application layer with the base layer.
Smart programmers can route around application-level blockages because the underlying physical infrastructure is still running. Code solves code problems. A programmer's cleverness is real, and in that constrained domain — application versus application — it is genuinely formidable.
The base layer is not a code problem. It is a physical one.
Consider the actual architecture of global data transmission. Approximately 99% of international internet traffic travels through undersea fiber-optic cables — a network of roughly 400 active cable systems at any given time, landing at a relatively small number of coastal cable stations. These stations are physical buildings. They have addresses. They have power requirements. They have a finite number of people who operate them.
This is not a secret. It is publicly documented infrastructure. The cable maps are published. The landing stations are known.
An application-layer disruption is a problem for a clever programmer. A kinetic disruption of base-layer infrastructure — whether through direct interference, emergency seizure authority, or electronic warfare techniques that have been declassified for decades — is a problem for everyone using the application layer simultaneously. There is no rerouting around a cable that has been physically severed or a station that has been physically secured.
The Garrett position does not fail because smart people lack ingenuity. It fails because physical reality has no patch cycle.
This is not a prediction of imminent infrastructure seizure. It is a structural observation: any sovereignty architecture that depends entirely on the good functioning of centralized physical infrastructure has an unexamined single point of failure. The convoy that acknowledges this before it matters is in a different position than the convoy that discovers it after.
III. The Swarm vs. The Stream — Rebuilding Communication on Antifragile Rails
If the stream can be kinetically disrupted, the architecture that replaces it needs a different physics.
The dominant model for data transmission is a stream: a directed flow from a central source to a receiving endpoint. A server. A platform. A cloud. Data lives somewhere, and you reach out and pull it. This architecture is efficient, convenient, and catastrophically fragile in a single-point-of-failure scenario, because the stream has a source — and sources can be located, secured, and stopped.
The alternative architecture is a swarm.
Most people encounter this model through BitTorrent — the protocol developed in 2001 that eliminated the central server by making every downloader also an uploader. In a BitTorrent swarm, a file does not live in one place. It is fragmented into pieces distributed across thousands of peers simultaneously. No single peer holds the complete file. No single peer needs to be online for the swarm to function. To "take down" a torrent, you would need to locate and simultaneously remove every peer — a task that scales impossibly as participation grows.
This is not merely a more convenient architecture. It is a different category of architecture. The stream is linear and hierarchical; disrupting the source disrupts everything downstream. The swarm is non-hierarchical and distributed; disrupting any node increases the relative importance of every other node.
NOSTR applies this logic to communication rather than file-sharing. In the NOSTR protocol, there are no central servers that own your identity or host your messages. There are relays — lightweight servers that any participant can run — and keys that belong entirely to the person who generated them. Your identity on NOSTR is your cryptographic key pair. No platform issued it. No platform can revoke it. If any relay goes offline, your messages are available from every other relay that has them. The swarm adapts.
For sovereign communications, this is not a feature preference. It is the difference between a communication channel that can be seized and one that cannot — because the latter does not have a single thing to seize.
Practically, this means the mature convoy's communication infrastructure should shift toward relay-based, key-authenticated, message-fragmented protocols wherever possible. Not because the centralized alternatives are currently blocked — they are not — but because building the habit now, while the infrastructure is cheap and the learning curve is friendly, is categorically different from attempting the migration under duress after the relevant application layer has been restricted.
The swarm does not require the stream to survive. Build on the swarm before you need it, so you never need it.
IV. The Privacy Layer — Safety Glass, Not Contraband
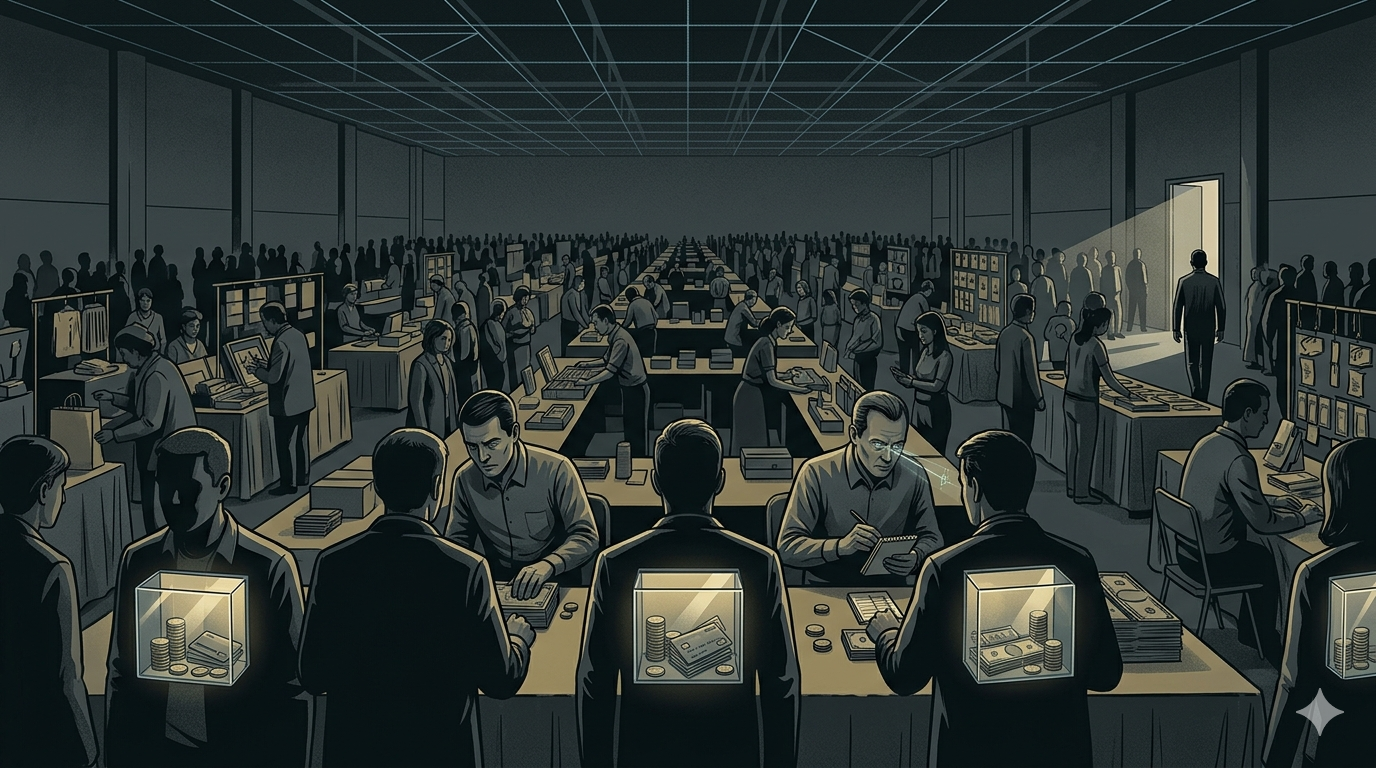
Picture a convention center floor. Hundreds of tables. Vendors selling everything from tools to produce to services. Buyers moving through the aisles with cash in their pockets, weighing options, negotiating on the fly.
Now add one change: every seller can see through every buyer's wallet. Not just the current balance — the full history. What they came in with. What they've already spent. What they bought three tables back and for how much. The behavioral trail as well as the current balance.
Watch what that single change does to the nature of trade.
The seller with five buyers in front of them immediately performs triage. Three came in with $100 — they're managed down, deprioritized, perhaps ignored entirely. Of the remaining two, both entered with $10,000. But one has already spent $9,000. He's nearly dry, possibly desperate for the last thing on his list, perhaps a big spender easy to read. The other still has all $10,000 intact — untouched, patient, a full capacity buyer. The seller now knows something the buyer did not intend to reveal: not just what they have, but who they are as a buyer. Their psychology. Their urgency. Their ceiling.
The seller no longer needs to make a case for the value of their goods. They need only calculate the buyer's breaking point.
This is the death of the fair market — not through malice, but through information. The moment the seller knows what you have, the negotiation ceases to be about the value of the thing being sold. It becomes an extraction calibrated to the depth of your pocket. The price is no longer determined by what the goods are worth. It is determined by the maximum amount the seller believes you will bleed before walking away.
This is not a hypothetical. It is already operating — in a softer form — every time you search for a flight.
The "bread crumbs" you leave across the internet — cookies, browser fingerprints, IP-derived location data, device type — are the convention floor equivalent of a glass wallet. A travel site that detects you have searched the same route five times reads that as urgency and may raise the price accordingly, pressuring you to buy before it climbs higher. An algorithm that identifies your device as a recent-model laptop in a high-income zip code assigns you a higher "willingness to pay" than a buyer on an older device in a lower-income area. Your neighbor on the same block, searching the same flight on the same day, may pay less — not because they negotiated harder, but because their digital profile suggested a lower ceiling.
Clear your cookies and you get a new session. Run a VPN and you obscure your location. Open an incognito window and the breadcrumb trail goes cold. These are imperfect workarounds, but they exist.
Now consider the same dynamic applied not to a browser session but to a KYC-linked financial identity — or, in its most complete form, a Central Bank Digital Currency. The seller no longer sees a browser. They see your tax identification number, your declared income, your transaction history, and your current balance. In real time. With no incognito mode available. No cookie to clear. No VPN that masks what the identity layer already knows.
The convention floor with glass wallets is not a future scenario. It is the destination of the current regulatory trajectory, expressed in the language of "financial security" and "fraud prevention." The KYC database is the infrastructure. The CBDC is the completion.
A persistent misframing follows any discussion of privacy tools — the reflex to treat Monero, VPNs, Tor, and encrypted messaging as tools of concealment, things people use because they have something to hide. That reflex implies transparency is the default of legitimate commerce and privacy is a deviation requiring justification.
This framing inverts the actual architecture of free trade.
Privacy is not a workaround. It is a foundational condition of voluntary exchange. You do not explain the contents of your wallet to the person at the next table before ordering coffee. You do not list every previous transaction to a vendor before agreeing on a price for their goods. Privacy in commerce is not suspicious — it is the default condition of trade between free people. The surveillance apparatus is the deviation. The KYC database is the anomaly. The requirement to produce a government-issued identity number before accessing basic financial services is the thing that requires justification, not the desire to transact without it.
The sovereign answer to the "nothing to hide" argument is not a defense. It is a correction: "Privacy is not required because I am a criminal. Privacy is required so that I am not economically predated upon by every vendor, bank, and tax collector I encounter. The man at the next table stays at his own table. My wallet remains my own business."
Think of privacy tools as safety glass.
Safety glass is not installed because a building's residents are planning something violent. It is installed because glass breaks and broken glass causes harm, and the cost of installing tempered safety glass is far lower than the cost of dealing with the consequences of broken shards. Nobody asks the building owner to justify their use of safety glass. Nobody implies they installed it because they expect trouble. It is simply a prudent engineering decision made by people who understand the physics of what happens when ordinary glass fails.
Monero is safety glass for financial transactions.
Unlike Bitcoin, where the blockchain is a public ledger and transaction graph analysis can — and routinely does — deanonymize wallet holders, Monero (XMR) builds privacy in at the protocol level. The sender is hidden. The recipient is hidden. The amount is hidden. This is not achieved through obscurity or workaround; it is achieved through cryptographic architecture — ring signatures, stealth addresses, and RingCT combining to make Monero transactions illegible to outside observers by design.
The safety glass analogy extends to the network layer. A VPN routes your traffic through an intermediary server, masking your originating IP address from the sites you visit and, more relevantly, from your Internet Service Provider's Deep Packet Inspection apparatus. DPI is the mechanism by which ISPs can identify the signatures of specific protocols — NOSTR relay connections, Tor circuits, encrypted traffic patterns — and throttle, block, or report them. A VPN renders your traffic generic: encrypted packets going to a server somewhere, indistinguishable from ordinary HTTPS traffic.
Tor goes further: it routes your traffic through three randomly selected relays, each knowing only the link immediately before and after it in the chain, so that no single relay can identify both your originating address and your destination. The cost is speed. The benefit is that the relationship between your identity and your traffic becomes computationally expensive to reconstruct.
These tools exist in a legal gray zone in some jurisdictions, but their use is not inherently illegal in most Western contexts, and their purpose — maintaining the privacy that free people are entitled to by default — is morally prior to any statute that restricts them.
The sheeple will not use these tools. The sheeple will accept the permissioned network because the permissioned network is frictionless and familiar and because they have not yet encountered a reason to care. This is not a moral judgment. It is an observation about statistical distribution. Most people make decisions based on convenience until convenience fails them.
The implication for the sovereign is structural, not ideological: the herd provides cover. When 99% of traffic is ordinary — cat videos, social media, streaming audio, email — the 1% that is encrypted, relay-fragmented, and privacy-hardened blends into the background noise. This is not deception. It is physics. A red flare in a night sky is impossible to miss. A red flare inside a fireworks display is invisible.
Build your perimeter while the display is still running.
V. The Cuban Shovel — Multi-functional Utility in a Grid-Down Scenario
Every tool in the sovereign architecture requires a grid.
Bitcoin requires electricity, internet, and functioning node infrastructure. NOSTR requires relays that are powered and connected. Monero requires a network to broadcast transactions across. Even gold-backed digital instruments require a platform, a power supply, and a data connection to initiate a settlement.
This is not a reason to abandon digital tools. It is a reason to hold them alongside something that does not share their dependency.
Consider the Cubans.
Under decades of embargo and supply restriction, Cuban artisans and mechanics developed a practice of radical material repurposing that became legendary in its ingenuity. Rum bottles, cut and sanded, became drinking glasses — not as novelties, but as functional tableware when no factory glass was available. Shovel steel — the carbon-steel alloy in an ordinary agricultural shovel — was repurposed for engine repair components, because its metallurgical properties were close enough to the required spec and the shovel was present while the correct part was not. The materials in hand were transformed into the materials needed, because the hands that held them understood multi-functional utility.
The logic is not primitive. It is the highest form of engineering discipline: design for what you have, not for what an uninterrupted supply chain would deliver.
Applied to sovereign wealth architecture, this logic generates a simple but load-bearing principle: any asset whose only utility is its face value in a functioning system is a liability when the system stops functioning.
A number on a screen — whether fiat in a bank account, Bitcoin in a custodied exchange wallet, or a gold-backed token on a KYC'd platform — is a permissioned asset. It requires the permission of the system that records it to be meaningful. If the system goes dark, the number goes with it. You hold a receipt with no claim to enforce.
A bar of silver in your physical possession does not require permission. It will not stop conducting electricity when the grid goes down. It does not need a relay to verify its mass. It will not be frozen because a compliance officer reviewed your transaction history. It is there, under your authority, with utility that exists independent of any external system.
The same logic applies across asset classes. Physical food production and storage. Water collection and purification infrastructure. Tools with mechanical utility that precedes electrical dependency — things that work because they have moving parts and the physical laws governing those parts have not changed. Hand tools. Non-motorized transport. Seed stock.
None of this is advocating for a return to pre-industrial life. It is advocating for a base layer of sovereign capability that the digital architecture sits on top of, rather than the reverse. The shovel does not replace the Bitcoin node. It ensures that when the Bitcoin node is online, the person operating it is not entirely dependent on the node's continued operation for basic function.
Possession is not the same as permission. The Trustee can revoke your permission. No one can revoke your possession without a confrontation in physical space — which is a categorically different kind of intervention than an account freeze.
This is not paranoia. It is the engineering principle of defense in depth: every critical system has a backup that operates on different dependencies than the primary. The backup for a grid-dependent wealth layer is a grid-independent one.
The shovel's steel does not require a relay. Neither does your silver.
VI. The Agorist Algorithm — Staying in the Gray
Samuel Edward Konkin III articulated the strategic logic of counter-economics with unusual precision. The key insight was not about resistance — it was about statistical irrelevance.
A state apparatus built for mass management is optimized for the average case. Its tools — tax collection, identity verification, financial surveillance, behavioral profiling — are calibrated for populations that behave predictably. The entire apparatus is designed around the assumption that the overwhelming majority of people will comply because compliance is frictionless and non-compliance is effortful.
This creates an arithmetic asymmetry.
When 99% of the population registers, declares, reports, and complies, the 1% who do not are not simply non-compliant — they are statistically invisible within the noise of the compliant majority. The surveillance system is calibrated for the 99%. Its anomaly detection is tuned to the patterns that stand out against the background of normal behavior. The 1% who have quietly stepped onto the perimeter are not running from the system. They are beneath its detection threshold — operating in a zone the system did not design for, because the system did not design for anyone who actually left.
This is the agorist algorithm: not confrontation, not resistance, not a red flare in a dark sky. Quiet departure into the gray.
The gray is not a hiding place in the pejorative sense. It is the natural color of the perimeter — the space between the two poles of the yin-yang that belongs to neither. It is Konkin's gray market made geometrically explicit: the zone of voluntary, peaceful, extralegal trade that starves the inverted trust not through combat but through economic irrelevance.
But staying in the gray requires active management. The gray zone has a border, and crossing it in either direction has different consequences.
Cross too far toward the black — toward transactions that are not merely extralegal but directly harmful, toward the kind of activity that provides the state with a legitimate grievance — and you lose the protection of the gray's neutrality. You become a visible target for reasons that have nothing to do with your political orientation.
Cross too far toward the white — toward full re-integration with the permissioned system, toward convenience at the cost of the three non-negotiables — and you are no longer on the perimeter. You are back inside the yin-yang, and the gravity of the center begins its work on you again.
The algorithm is: stay in the gray. Transact in the gray. Build your relationships in the gray. Let your economic life conduct itself, as much as possible, in the zone that is beneath the detection threshold of the apparatus designed to monitor the 99%.
Digital Camouflage
Staying in the gray has a technical expression that Konkin did not have available to him: digital camouflage.
The surveillance apparatus does not only monitor the content of transactions. It monitors the patterns of behavior — the metadata that surrounds the content. An IP address that connects exclusively to privacy-tool nodes is flagged. An account that uses no mainstream services is flagged. A device that emits no recognizable consumer behavioral signature is flagged. Anomalies are expensive to investigate individually, but automated systems can flag them at scale and queue them for human review at a later time.
Digital camouflage does not require you to surrender your privacy tools. It requires you to embed them within a behavioral signature that reads as ordinary. Ordinary people use YouTube. Ordinary people have streaming subscriptions. Ordinary people buy things through conventional channels for the items where that is the path of least resistance and the privacy cost is low. The sovereign is not a hermit. The sovereign is someone whose critical transactions and communications happen in privacy-hardened channels, surrounded by enough ordinary background noise that the overall behavioral signature does not stand out as anomalous.
This is the data equivalent of hiding an encrypted shard inside a cat video — technically documented in steganographic research, and conceptually applicable at the behavioral level. Your Monero transaction does not have a neon sign above it because your morning is otherwise indistinguishable from anyone else's.
This is not compromise. It is craft. The difference between a soldier and a spy is not commitment to the mission — it is the craft of remaining undetected while the mission is executed.
VII. The Sovereign Trinity, Hardened
The previous article introduced the sovereign trinity: Bitcoin for velocity, hard assets for anchor, NOSTR for marketplace. The hardening layer adds specificity to each.
Bitcoin remains the engine for global value transport. The hardening addition: self-custody is not optional. Coins on an exchange are the exchange's coins — a permission that can be revoked, a balance that can be frozen, a ledger entry that can be altered. Coins in a hardware wallet, held by a private key that exists only in your physical possession and your memory, are yours in the same sense that your shovel is yours. Custody is sovereignty. Delegation is the first step back toward the Trustee relationship.
Monero (XMR) enters the hardened architecture as the privacy layer for local and extralegal trade. Where Bitcoin's public ledger makes large-scale financial analysis possible for anyone with sufficient blockchain analytics capability, Monero's protocol-level privacy makes it genuinely illegible. For the gray market transaction — the exchange of value between people who have not registered their trade with a third party — illegibility is not a preference. It is the condition that makes the gray zone viable.
NOSTR carries the communications layer. The hardening addition: run your own relay if you can. A relay you operate is a relay that cannot be administratively deplatformed. The NOSTR protocol is already antifragile at the network level — but your personal resilience within that network increases with each element of the infrastructure that you control directly.
Physical assets — gold, silver, land, and the Cuban shovel's extended family — are the base layer on which everything digital rests. The hardening principle: the ratio of physical to digital should be calculated against a grid-down scenario, not a grid-functioning scenario. Not because the grid is imminently going down, but because a base layer that only functions when everything is working is not a base layer. It is a dependency.
Mesh networking is the last layer most people have not begun thinking about. Grassroots physical networks — devices that route packets locally without requiring the central Data Pipeline — exist and are deployable at community scale with modest technical investment. goTenna, Meshtastic, and similar technologies allow devices to form ad-hoc mesh networks that route messages through direct radio connection rather than internet infrastructure. The range per node is limited. The coverage per community-scale deployment is not. A neighborhood with sufficient mesh node density can communicate internally even if the undersea cables have been severed and the nearest internet exchange is dark.
This is not science fiction. It is off-the-shelf hardware with mature software, already deployed in disaster response contexts around the world. The sovereign application is simply to extend that deployment before the disaster scenario requires it.
A Timing Note for the Convoy
This article is addressed to those who have already completed the work described in the first one: a stable foundation, a consistent revenue stream operating at least partially on the perimeter, and a working understanding of the sovereign trinity at a conceptual level.
If you are still building that foundation — if the primary financial question right now is how to generate consistent income rather than how to harden the infrastructure around existing income — this article is a compass heading, not today's operating instruction. File it. Return to it when the base is solid.
The hardening architecture described here is not urgent in an emergency sense. It is urgent in a compound interest sense. The cost of building these capabilities before they are needed is low. The cost of attempting to build them under duress, in the context of a degraded network, with unfamiliar tools and a learning curve you have not yet run — that cost is categorically higher. Possibly prohibitive.
This is not about fear. It is about the same engineering logic that makes a seatbelt sensible: the probability of needing it at any given moment is low, the cost of wearing it is trivial, and the cost of not having it on the occasion you need it is absolute.
Conclusion: The Perimeter Is the Purpose
There is a version of the sovereign conversation that gets stuck on the adversarial frame — them versus us, the state versus the people, the Trustee versus the Beneficiary in perpetual conflict. That frame is understandable. The paper trail of breach is real, and naming a breach requires naming the party that committed it.
But the perimeter you are building is not primarily about them. It is primarily about what you are building.
The agora is old. It predates the surveillance apparatus by millennia. Free people exchanging value on their own terms — without permission, without a toll, without a Trustee claiming authority over the transaction — is not a radical innovation. It is the baseline condition of human commerce, temporarily interrupted by an elaborate system of intermediation that has mistaken its delegated authority for ownership.
The sovereign trinity is a restoration project, not a revolution. The Bitcoin node, the silver bar, the NOSTR relay, the Monero wallet, the mesh device in the garage — none of these are weapons in a political conflict. They are the tools of ordinary life, reconstituted outside the permissioned system that has been built around ordinary life without the beneficiaries' consent.
When the Trustee acts as owner, the Beneficiary's response is not to fight for control of an institution that has already been captured. It is to walk around the institution entirely — to find the road that does not pass through the center, and to build along it, steadily, with the people who understand what they are building.
The perimeter is not the fringe. It never was. The fringe is the system that demands permission before it allows you to transact.
The perimeter is where the pencil gets made by free people.
Build the wall. Hold the line. The road is the purpose.
⚠️ Experimental Compass Heading — Admonition for the Mature Convoy
This article is a framework, not a finished system. The toll booths described here are real — not metaphorical. The legislative architecture for digital identity, financial surveillance, and network control is advancing across multiple jurisdictions simultaneously, and the precedent established by "temporary emergency" frameworks has a documented historical pattern of permanence.
The military has historically been deployed as a tool of rogue Trustee operations — domestically and globally — and the inverted trust does not announce itself as an inversion. It announces itself as a security measure.
None of the tools described here are illegal in most jurisdictions where this article's readers reside. The privacy imperative is not a call to criminality. It is a call to exercise the rights that Proclamation 2402 and the constitutional compact already recognize — the rights of sovereign citizens who have not surrendered them.
Build your physical base layer first. Then your digital layer. Then your mesh. The order matters because if the grid goes down while you are in the middle of the digital step, the physical base is what you will be living on.
The only road that does not go through a toll booth is the one built on uncompromising principles: Natural Law, Physical Possession, and the Gray that belongs to those patient enough to stay in it.
No KYC. No usury. No fiat.
This is an experimental framework — in development, open to revision, and not financial or legal advice. It is a compass heading: the direction of travel for the convoy that has already decided the toll booths are unacceptable and the perimeter is worth hardening.
Further Reading & Resources
- Samuel Edward Konkin III — New Libertarian Manifesto (1980)
- FDR — Proclamation 2402, May 27, 1940
- NOSTR Protocol — nostr.com
- Monero Project — getmonero.org
- Meshtastic Project — meshtastic.org
- Albert O. Hirschman — Exit, Voice, and Loyalty (1970)
- The Only Road That Doesn't Go Through a Toll Booth — digitalstartuplifestyle.com





